Clearbridge helps businesses with more than just tips to protect you from fraudulent email scams. We help by leading your digital strategy efforts through investments in technology. Connect with us to learn more about how Clearbridge can help your business by clicking here. Talk soon!
“I’D NEVER FALL FOR THAT.”
Fraudulent and malicious emails are on the rise, and for one simple reason: they work.
No, they don’t fool 100% of us—they don’t even fool a tenth of us. But every time one in a thousand people falls for an email scam, a hacker knows that these emails can work. And so they figure out what worked and replicate it again and again.
Now you may have never fallen for a scam email, but that doesn’t mean you won’t. Hackers are a little sharper than they used to be.
Gone are the days of the Nigerian prince offering wealth in exchange for your banking info.
We’re at the point now where hackers are sending emails posing as trusted institutions, brands, bosses, coworkers, and friends.
And people are falling for it. Even people like you and me.
I’m going to show you three super simple and IMPORTANT ways to protect yourself from becoming a victim of fraudulent emails.
Worth Noting: You might be thinking, “shouldn’t our spam filters keep these types of messages from my inbox?” In short, yes, but no system is 100% effective, and any system that is puts your legitimate email at risk of being blocked too. That’s why it’s best to educate yourself on what to watch for when you inevitably see these types of messages in your inbox.
TIP #1: CHECK THE ‘FROM’ EMAIL ADDRESS
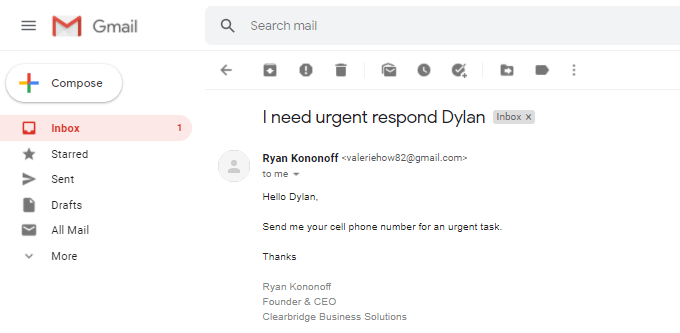
Here’s a great example:
Just because an email “looks” like it’s from your CEO doesn’t mean it really us.
I recently received the email pictured below from Ryan, our CEO.
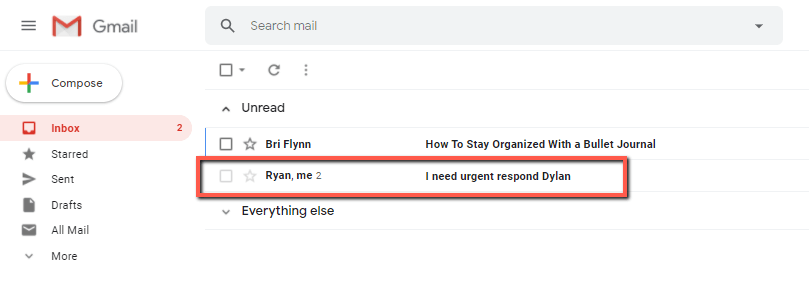
It showed up in my inbox with Ryan’s name. The subject line was a little suspect as it contained a typo. (That should have been my first tip-off.)
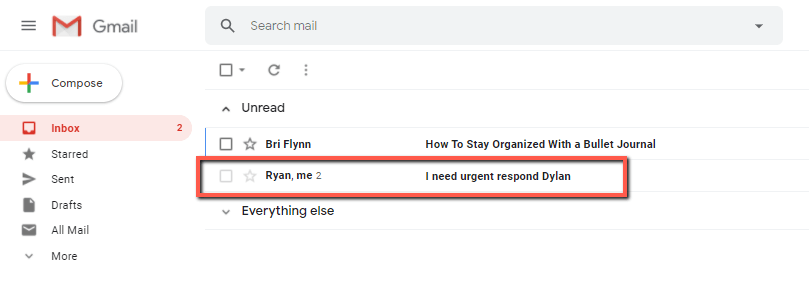
I opened the email and it immediately seemed odd. Ryan would have sent me a direct message rather than an email if he actually needed my phone number.
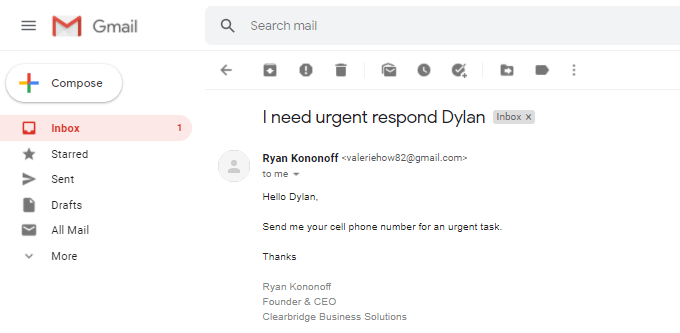
By now I was very suspicious.
Next, I looked at the actual sender’s email address—and that was all the evidence I needed to confirm my suspicions: this wasn’t an email from Ryan. A spammer attempted to obtain personal information from me by acting as Ryan.
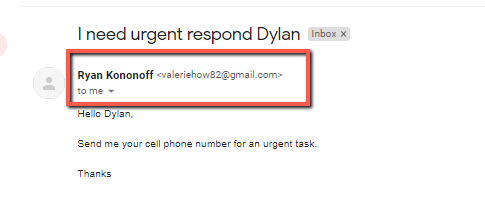
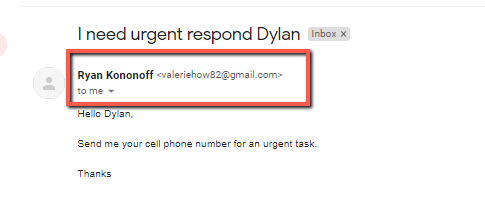
This form of manipulation is called social engineering, and it’s the number one reason you are likely to fall victim to an email scam.
By simply checking the ‘From’ address, I was able to immediately detect this wasn’t an email from Ryan but from someone with malicious intent.
TIP #2: ALWAYS CHECK LINKS BEFORE CLICKING
The previous email example didn’t have any links in it, but let’s take a look at this email I received from a coworker. You’ll see the arrow pointing to the linked text.
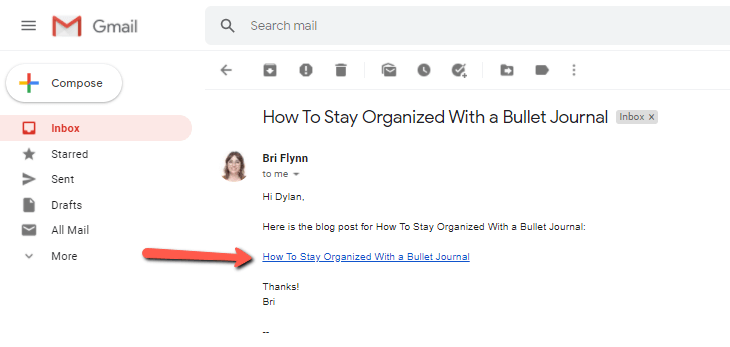
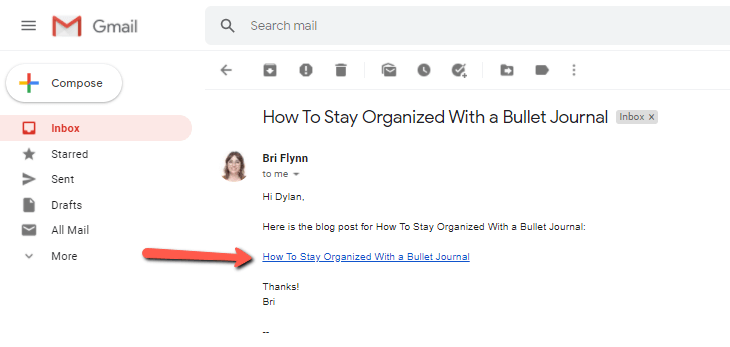
Everything in the email looks secure, including Bri’s email address—but how can I confirm the link is safe?
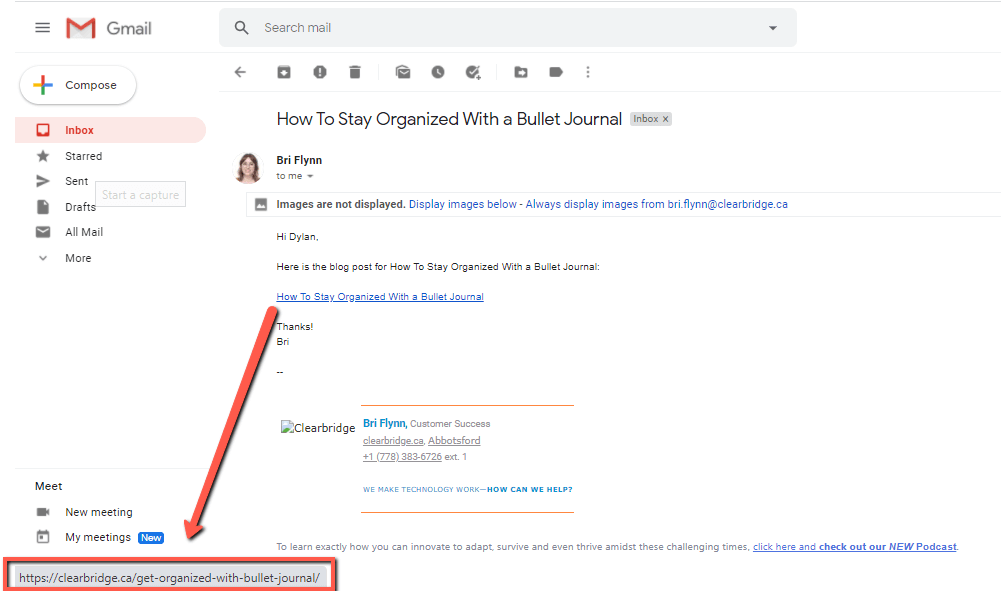
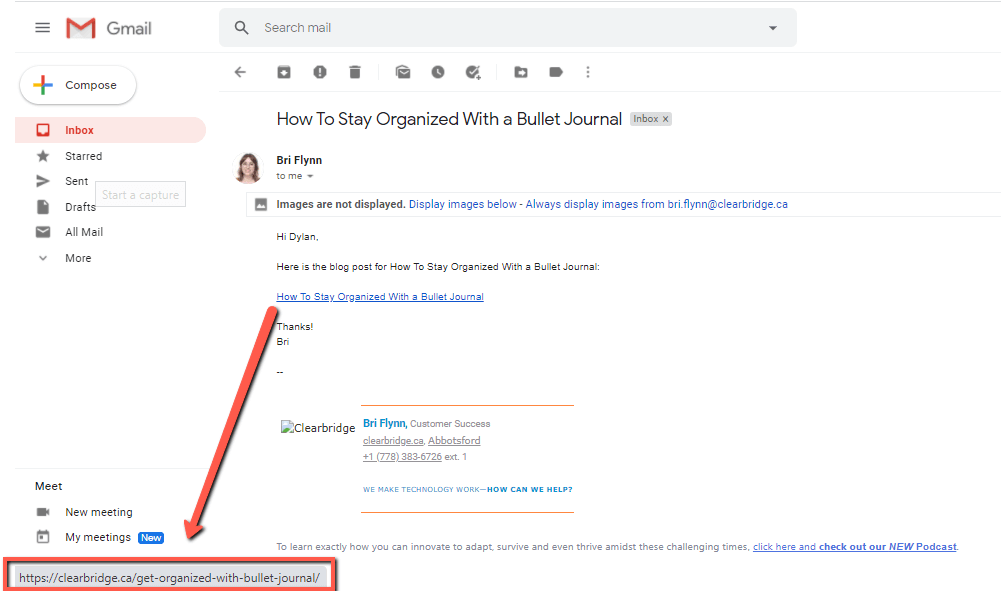
By hovering your mouse over the text, you’ll see a link appear on the bottom left corner of your window. That’s a preview of the link you’re about to click on.
TIP: You can get a link preview on your phone if you hold your finger over the link.
If you don’t recognize the link or if it looks suspicious in any way—don’t click it. The best rule of thumb to avoid falling for a scam is if it looks and feels suspicious, it probably is.
ESPECIALLY if you don’t recognize the sender.
TIP #3: NEVER DOWNLOAD ATTACHMENTS FROM AN UNRECOGNIZED OR UNCONFIRMED SENDER
This tip can’t be stressed enough!
Why?
Because hackers can access your computer and network to potentially cause serious damage if you happen to innocently download their malware believing it to be a file attachment, PDF, or zip file.
It’s really important you DO NOT download any files without checking and confirming the sender is from an email address you know and trust.
In the first example with the email from the sender posing as our CEO, had there been any attachments in that email, I may have been tempted to quickly download them had I not seen the ‘from’ email address wasn’t actually Ryan.
Be. Vigilant. Think twice—then think again—before downloading attachments.
WRAPPING UP
These are just a few examples of ways hackers are attempting to hijack information and access your data. If you follow these three tips of how to protect yourself from fraudulent emails and remain extremely vigilant and suspicious of anything that comes into your inbox, you’re going to be a huge step ahead.
And don’t hesitate to reach out to us if you have any concerns about your email or data security. We’d love to help!
Clearbridge Business Solutions helps businesses by leading their digital strategy efforts through investments in technology. If you’d like to learn more about how Clearbridge may be able to help your business, connect with us by clicking the button below. Talk soon!

